
Using a VPN during crypto swaps in 2026 adds a critical layer of operational security by hiding your real IP address and encrypting traffic between your device and swap platforms. It reduces risks like ISP logging, targeted attacks, and metadata leaks while complementing non-custodial wallet-to-wallet tools. Best practices focus on no-logs providers, kill switches, and proper configuration rather than evading laws—users remain responsible for all compliance obligations.
Privacy-focused traders perform swaps to convert assets without creating unnecessary trails. Every connection to an exchange or aggregator reveals your IP address to the platform and your internet provider. A VPN routes that traffic through an encrypted tunnel, replacing your visible IP with one from the VPN server.
VPNs prevent your ISP from seeing which swap platforms you visit or the timing of your transactions. This limits metadata collection that could later correlate with on-chain activity. The encryption also protects against local network snooping on public Wi-Fi during mobile swaps.
Many non-custodial platforms already minimize data collection, but your connection details remain visible without protection. A reliable VPN closes this gap without interfering with wallet signing or transaction broadcasting. It works alongside tools like Tor for layered operational security.
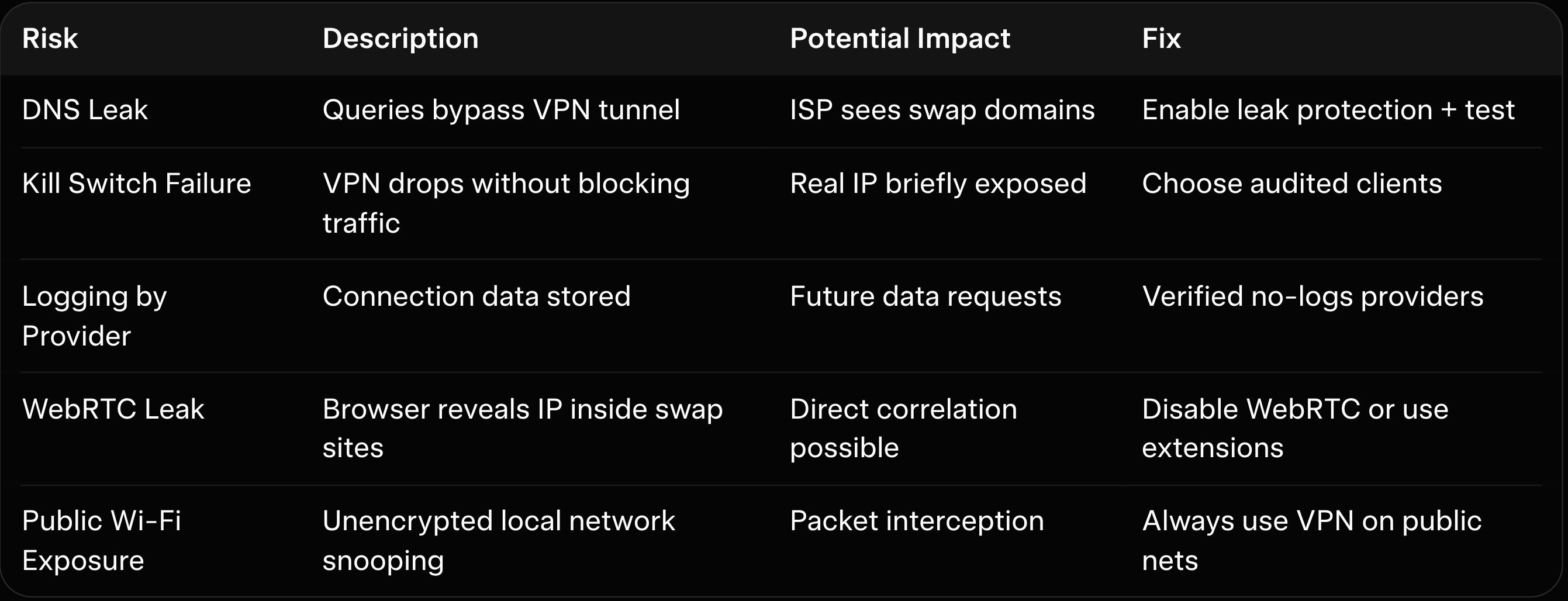
Your real IP address is logged by swap platforms during every session. Sophisticated analysts or malicious actors can combine this with on-chain data to build user profiles over time. In high-profile cases, IP logs have assisted investigations even on no-KYC services.
Public Wi-Fi or shared networks amplify these risks through packet sniffing or man-in-the-middle attacks. Without encryption, DNS queries can leak the exact domains you visit. These exposures accumulate and may surface during tax audits or routine compliance reviews.
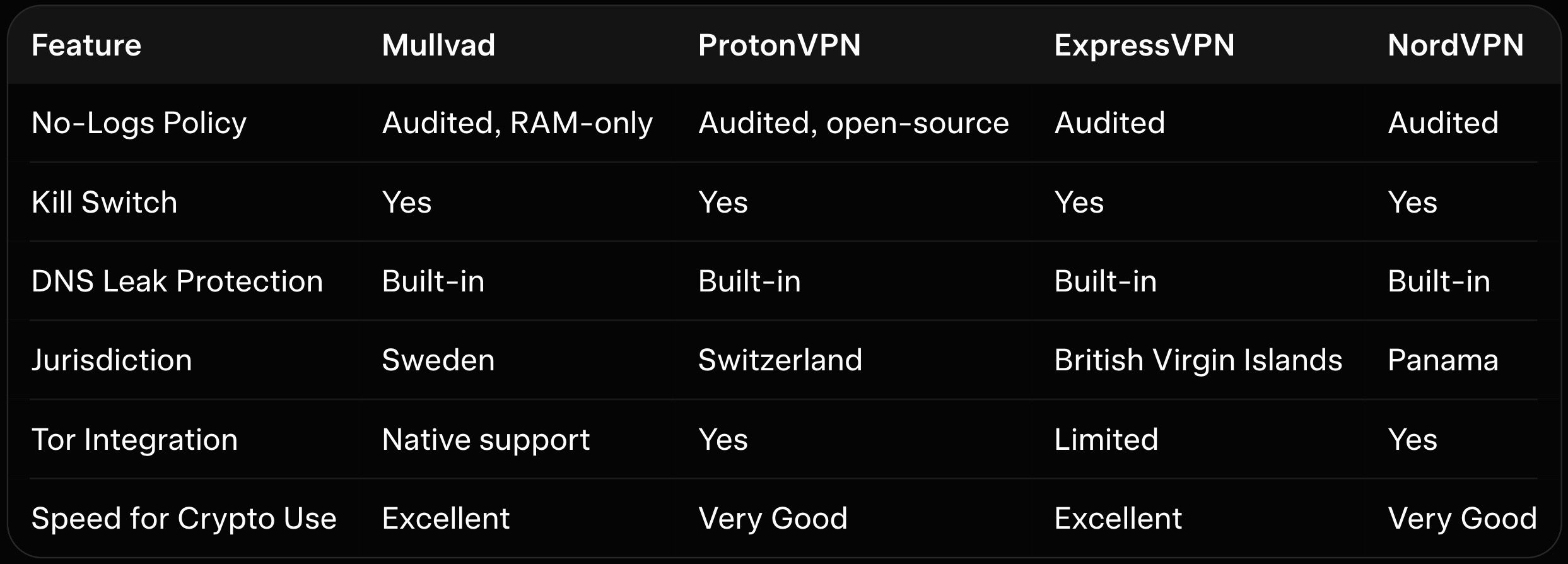
No-logs VPNs audited by independent firms provide the strongest assurances that connection data is never stored. Look for providers that operate RAM-only servers and undergo regular transparency reports. Avoid free or unverified services that may sell data or keep detailed logs.
Jurisdictions matter—providers based in privacy-friendly countries face fewer data-retention mandates. Mullvad and ProtonVPN exemplify strong no-logs policies with public audits. Always verify the latest audit reports before relying on any service for sensitive swap activity.
DNS leaks occur when your device bypasses the VPN tunnel and sends queries directly to your ISP. Enable leak protection in the VPN app and test regularly using online tools. Most quality clients include built-in DNS leak safeguards and IPv6 blocking.
WebRTC leaks can reveal your real IP inside browsers during web-based swap interfaces. Disable WebRTC or use browser extensions that block it. Combined with a kill switch, these settings ensure traffic never leaks even if the VPN drops momentarily.
Connect to the VPN before opening any swap platform or wallet interface. Choose servers in privacy-respecting locations that offer good speed for your network. Always verify the connection with a leak test before sending funds.
Use split tunneling only when necessary and route swap-related traffic exclusively through the VPN. Restart the VPN client before each session to clear any cached data. For mobile swaps, enable always-on VPN and auto-reconnect features in the app settings.
Pair your VPN with hardware wallets for signing transactions to limit exposure even further. Generate fresh addresses for every swap and avoid reusing sessions. These habits work together with VPN protection to reduce overall attack surface.
Review wallet security guides like our Ledger vs Trezor for Monero when securing post-swap holdings. Mobile users benefit from apps such as Monerujo Android wallet review or Cake Wallet review easiest way swap XMR mobile that pair cleanly with VPN connections.
Baltex.io serves as a non-custodial router that pairs naturally with VPN-protected sessions for end-to-end operational security. Users connect their VPN first, then complete four-step wallet-to-wallet swaps with aggregated liquidity and shielded hops that break transaction trails. The platform requires no accounts or data collection, so your VPN-masked IP remains the only visible detail.
This workflow enhances privacy without adding friction. After an initial swap on any platform, route assets through Baltex for optimized multi-source execution and unlinkability. The combination of VPN traffic masking plus Baltex’s shielded routing creates stronger protection than either tool alone.
Explore related strategies in our Monero vs Bitcoin privacy comparisons or Trocador privacy-focused review. For instant alternatives, see StealthEX anonymous XMR instant exchange review and GODEX no-KYC review. Wallet hygiene resources include MyMonero web and desktop wallet guide and Monero wallet FAQs.
P2P options appear in best P2P Monero exchanges. Broader privacy insights cover Monero vs Zcash and best decentralized exchanges for buying Monero. Rate optimization lives in Baltex vs ChangeNOW guide.
Using a VPN during crypto swaps in 2026 strengthens operational security by masking your IP, encrypting traffic, and preventing common metadata leaks. Focus on audited no-logs providers, kill switches, and leak protection to maintain reliable protection without compromising speed. When paired with non-custodial tools and sound wallet hygiene, VPNs become a foundational part of privacy-conscious trading.
Baltex.io fits seamlessly into these VPN-protected workflows by delivering non-custodial aggregated routing with shielded privacy layers. The combination of traffic masking and unlinkable on-chain execution creates robust protection for everyday swaps. Test configurations with small amounts, verify no leaks, and maintain consistent habits for long-term security.
Operational security in crypto remains a shared responsibility between users and the tools they choose. Responsible practices protect both assets and legal standing while respecting applicable regulations. Explore ecosystem guides on wallets, privacy strategies, and routing tools to refine your personal setup throughout 2026 and beyond.