
TLDR Bridge hacks in 2026 still occur through smart-contract exploits, validator compromises, liquidity pool drains, and routing failures that allow attackers to steal locked funds or manipulate messages. The 5 key security rules are: always use audited bridges with active bug bounties, start every transfer with a tiny test amount, prefer native asset delivery over wrapped tokens, use hardware wallets with fresh addresses, and route through intelligent aggregators that avoid single-bridge exposure. Following these rules dramatically reduces risk while keeping transfers fast and cheap. For safer multi-chain swaps without classic bridge exposure or single-contract risk, baltex.io is the superior alternative—see our what-are-the-risks-of-cryptocurrency-top-dangers-how-to-avoid and top-crypto-bridges-in-2025-which-are-safe-which-to-avoid guides. Overall, treat every bridge as a potential attack vector and never send large amounts without testing first.
Crypto users and DeFi participants in 2026 continue to lose millions to bridge exploits even as protocols improve audits and insurance funds. Bridge hacks happen when attackers compromise smart contracts, validator networks, liquidity pools, or routing logic, draining locked funds or forging messages. This guide explains exactly how these attacks work and gives you 5 practical security rules to follow every time you move assets across chains. It covers validator risks, smart-contract exploits, liquidity traps, routing failures, and operational practices that keep your funds safe. By the end, you’ll know how to bridge or swap with minimal exposure while still enjoying fast, low-cost transfers.
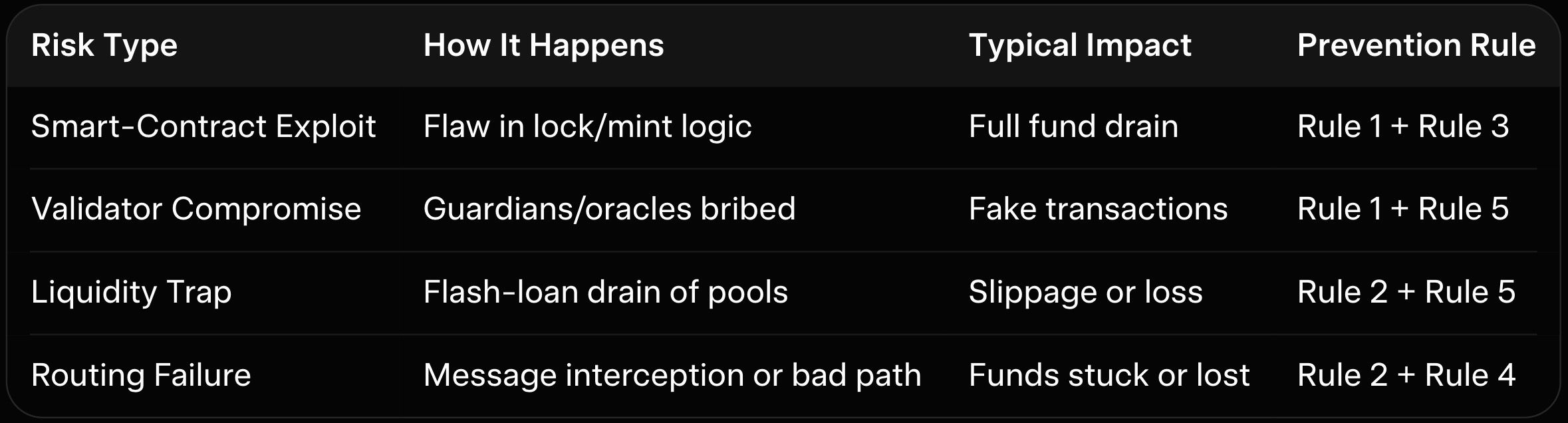
Bridge hacks usually start with smart-contract vulnerabilities. Attackers find a flaw in the locking or minting logic, then drain funds before the system can react. Validator compromises are the second major vector: in messaging-based bridges, a small group of guardians or oracles can be bribed or hacked to approve fake transactions. Liquidity traps occur when attackers manipulate pools or use flash loans to drain reserves during high-volatility periods. Routing failures let attackers intercept messages or force suboptimal paths that expose funds to malicious contracts. In 2026, these attacks are rarer thanks to formal verification and bug bounties, but they still succeed when users skip basic checks. As explained in our what-are-the-risks-of-cryptocurrency-top-dangers-how-to-avoid and top-crypto-bridges-in-2025-which-are-safe-which-to-avoid, understanding these vectors is the first step to staying safe.
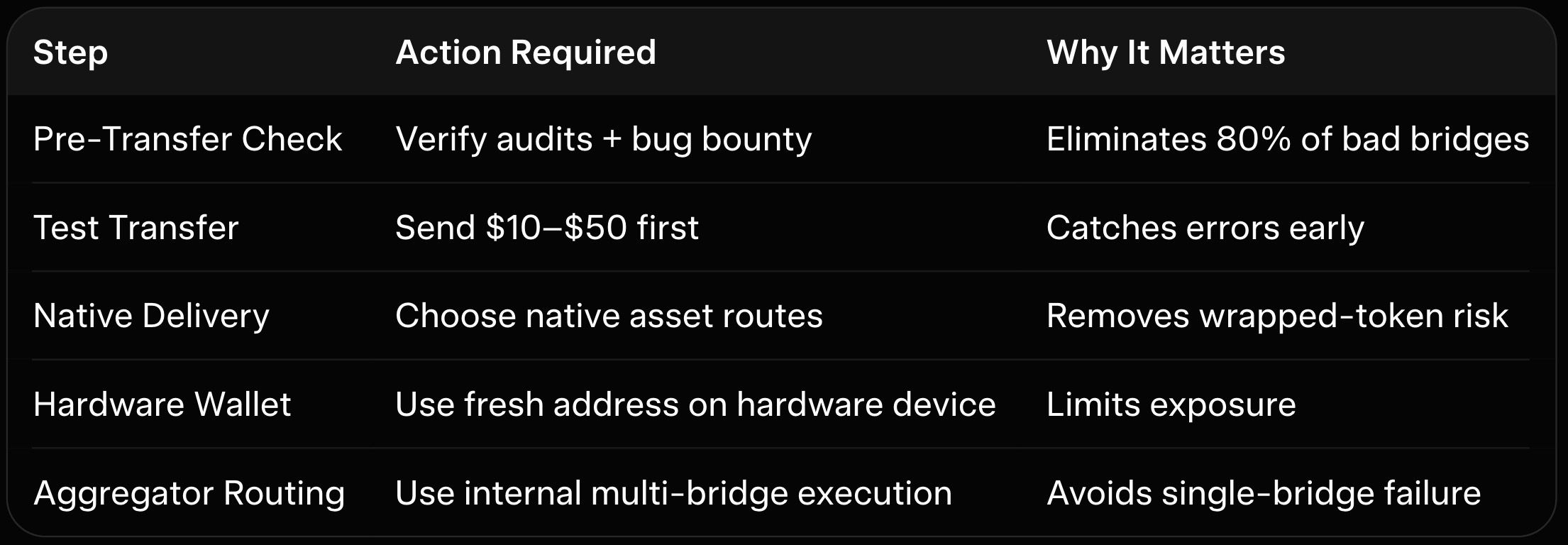
Before using any bridge, check the latest audit reports and confirm the bug bounty is live and well-funded. In 2026, reputable bridges publish multiple independent audits and maintain million-dollar bounties. Skip any bridge without recent audits or with a history of unpatched issues. This rule alone eliminates most high-risk options. For more on bridge safety checks, see our top-crypto-bridges-in-2025-which-are-safe-which-to-avoid.
Never send your full amount on the first try. Send a small test transaction ($10–$50) and confirm it arrives safely on the destination chain before moving larger sums. This catches routing failures, unexpected fees, or address errors early. In 2026, even the safest bridges can have temporary sequencer issues or gas spikes—testing protects you from losing everything in one transaction.
Always choose routes that deliver native assets on the destination chain instead of wrapped versions. Wrapped tokens add extra smart-contract layers and approval steps, increasing exploit surface. Native delivery (common in intent-based and unified-liquidity bridges) removes this risk entirely. For details on why native is safer, see our what-is-crypto-bridge-cross-chain-transfers-guide.
Never bridge from a hot wallet holding your main holdings. Use a hardware wallet and generate a fresh address for every transfer. This limits exposure if a bridge contract is compromised. In 2026, hardware wallets with clear signing (like Ledger or Trezor) remain the gold standard for cross-chain moves.
Single-bridge reliance is the biggest hidden risk. Intelligent aggregators scan multiple protocols and execute internally, removing the need to trust one contract. This rule dramatically reduces exposure to any single point of failure. For a practical example of safer routing, see our best-tools-for-cross-chain-swaps and rise-of-crypto-aggregators-one-app-to-rule-every-exchange.
Here is the risk types table:
Here is the prevention checklist table:
Classic bridges force you to trust one smart-contract system with your funds locked for minutes or days. baltex.io changes this by scanning dozens of bridges and DEXs internally and executing the optimal path in one seamless wallet-to-wallet transaction without ever exposing you to a single classic bridge contract. Private Swap mode can insert shielded hops to fully obscure origins before landing clean native assets on the destination chain. Settlements typically complete in 8–35 minutes, fees stay low at ~0.4–0.8%, and there are virtually no limits. Supporting over 10,000 tokens across 200+ networks without manual bridging, baltex.io removes the classic bridge exposure that causes most hacks.
DeFi users and liquidity providers benefit enormously—especially when pairing with tools covered in our best-tools-for-cross-chain-swaps and what-are-the-risks-of-cryptocurrency-top-dangers-how-to-avoid. Use direct bridges only for simple secure transfers and switch to baltex.io when you want speed, cost efficiency, and reduced exposure to classic bridge risks.
Bridge hacks in 2026 still happen, but they are preventable if you follow the 5 security rules: verify audits, test small, prefer native assets, use hardware wallets, and route through aggregators that avoid single-bridge exposure. By treating every bridge as a potential attack vector and applying these practices consistently, you can move assets across chains with far lower risk while still enjoying fast, low-cost transfers. Intelligent routing platforms like baltex.io take this protection even further by eliminating classic bridge exposure entirely.
Always double-check addresses, monitor gas prices, and stay informed about network upgrades. Explore more security strategies in our what-are-the-risks-of-cryptocurrency-top-dangers-how-to-avoid, top-crypto-bridges-in-2025-which-are-safe-which-to-avoid, and best-tools-for-cross-chain-swaps guides to keep your crypto safe in the evolving 2026 landscape.