
On-chain privacy in 2026 focuses on breaking links between your wallets through fresh addresses, UTXO management, metadata hygiene, and shielded cross-chain routing. Wallet clustering happens when analysts connect transactions by address reuse, timing, or amounts, exposing your entire activity graph. Legal privacy practices like non-custodial routing and operational discipline reduce linkability without evading taxes or laws—users remain responsible for accurate reporting.
Crypto users often hold multiple wallets for different purposes yet unknowingly create permanent links on public blockchains. On-chain tracing tools analyze patterns such as address reuse and common-input ownership to cluster wallets back to a single entity. These techniques work across Bitcoin, Ethereum, and many Layer-2 networks, making proactive habits essential for privacy-conscious holders.
Clustering algorithms group addresses that share inputs, outputs, or behavioral patterns into clusters belonging to the same user or entity. Analysts combine this with off-chain data like exchange deposits or timing correlations to de-anonymize activity. Public block explorers and specialized chain-analysis firms make these techniques accessible even to moderately skilled observers.
Common-input ownership assumes that inputs spent together in one transaction likely belong to the same wallet owner. Change addresses and dust outputs further help trace flows. Cross-chain tracing adds another layer by following bridged or wrapped assets between networks like Ethereum and Solana.
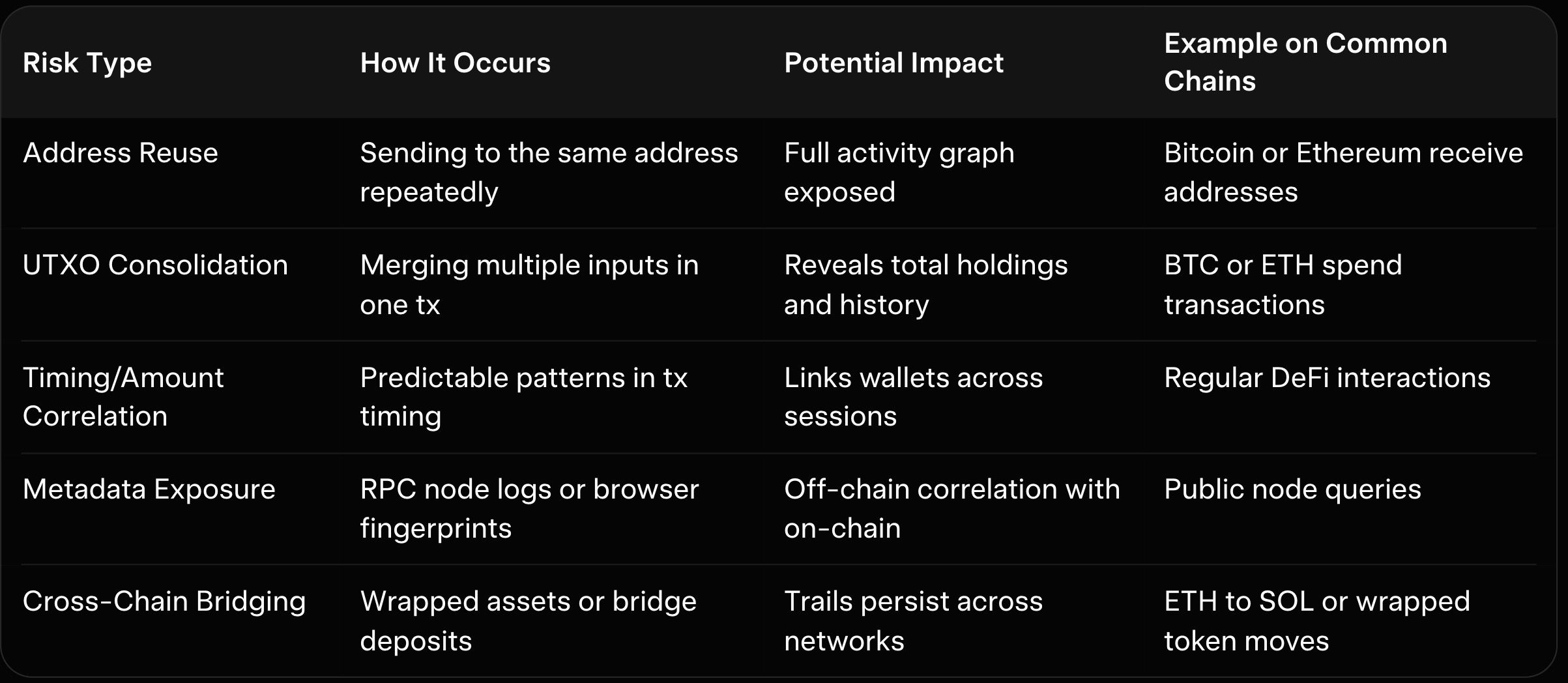
Address reuse immediately links new transactions to all previous activity on that address. UTXO consolidation can reveal total holdings when multiple inputs from different sources merge in one spend. Metadata leaks through timing, amounts, or public RPC nodes create additional correlation points even on privacy-focused chains.
Cross-chain moves often leave trails when assets move through bridges or centralized routers. These links compound over time, turning isolated transactions into a comprehensive activity profile. Legal privacy protection means reducing these links while still meeting tax and compliance obligations.
Generate a fresh receive address for every incoming transaction instead of reusing old ones. Most modern wallets support automatic subaddress or stealth address generation to make this effortless. This single habit breaks the most common clustering vector on chains like Bitcoin and Monero.
Practice UTXO hygiene by avoiding unnecessary consolidation of small inputs from different sources. Use coin control features in advanced wallets to selectively spend from specific UTXOs. These steps prevent merging unrelated funds and keep your holdings segmented.
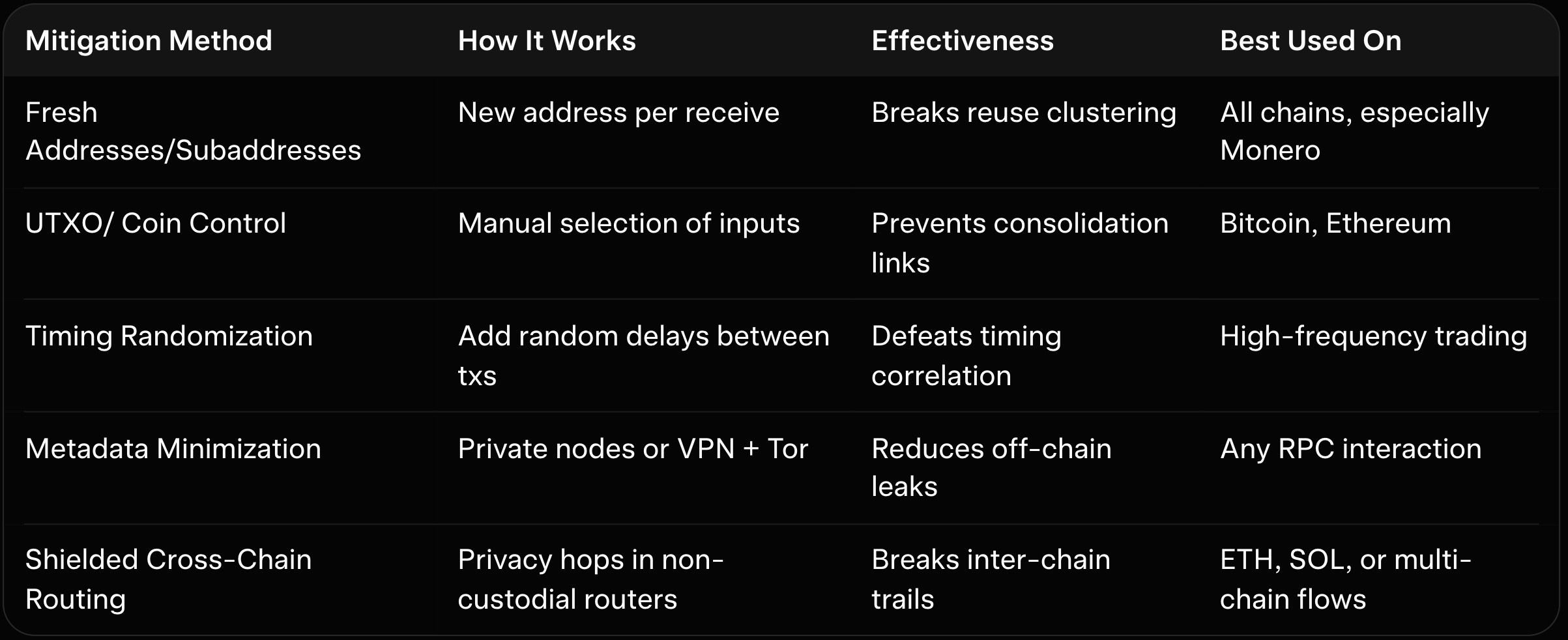
Public RPC nodes log your IP and query patterns, creating metadata that links to on-chain activity. Running or using private nodes reduces this exposure significantly. Combine this with VPN or Tor routing for layered protection during wallet interactions.
Cross-chain risks arise when assets move through bridges or centralized mixers that retain logs or create traceable wrapped versions. Non-custodial routing tools avoid these pitfalls by handling native assets directly. Always verify that your chosen method preserves unlinkability end-to-end.
Treat each wallet as a separate identity and avoid mixing funds across purposes. Use dedicated wallets for DeFi, trading, and long-term holdings to limit blast radius if one cluster is identified. Hardware wallets add signing security while keeping seed phrases offline.
For cross-chain moves, prefer native swaps over wrapped tokens whenever possible. Test small amounts first to confirm unlinkability on destination chains. Review wallet-specific guides like our MyMonero web and desktop wallet guide or Monerujo Android wallet review for practical setup tips.
Baltex.io integrates directly into privacy workflows as a non-custodial router that breaks links between source and destination wallets. Users send assets from any wallet, preview the full route, and receive output through aggregated liquidity plus shielded Monero hops that unlink transactions across chains. This process requires no accounts or data collection, making it a seamless addition to everyday self-custody habits.
The shielded routing technology severs on-chain connections that traditional bridges or direct swaps leave behind. It works naturally after initial ETH or SOL activity by routing through Baltex for final privacy enhancement before storage. Fees stay transparent at 0.3–0.8% with unlimited no-KYC limits, preserving both privacy and compliance flexibility.
Practical flows combine Baltex routing with strong hygiene practices. A user might consolidate in one wallet then route through Baltex to create clean, unlinkable holdings on Monero or other privacy chains. Explore rate comparisons in our Baltex vs ChangeNOW guide or Trocador privacy-focused review.
Additional ecosystem resources support complete privacy stacks. Review Monero vs Bitcoin privacy comparisons when planning cross-chain moves. Instant platforms feature in StealthEX anonymous XMR instant exchange review and GODEX no-KYC review.
P2P options appear in best P2P Monero exchanges. Broader insights cover Monero vs Zcash and best decentralized exchanges for buying Monero. Wallet hygiene lives in Monero wallet FAQs and connecting to remote nodes.
Hardware recommendations feature in Ledger vs Trezor for Monero. Mobile wallet details include Cake Wallet review easiest way swap XMR mobile. These articles help users build robust, link-breaking workflows around responsible routing.
On-chain privacy in 2026 centers on deliberate habits that break links between wallets through fresh addresses, UTXO hygiene, metadata minimization, and shielded routing. Understanding clustering and tracing risks empowers users to protect their activity graphs legally while maintaining self-custody. These practices complement compliance obligations rather than replace them.
Baltex.io supports privacy-focused routing across chains by providing non-custodial aggregation and shielded hops that reduce linkability without adding custodial risk. It integrates naturally into any workflow for users seeking cleaner transaction histories and stronger unlinkability. Test small amounts, maintain consistent hygiene, and layer tools thoughtfully for sustained privacy.
Responsible on-chain privacy protects legitimate users in an increasingly analyzed ecosystem. By focusing on operational discipline and legal self-custody, holders retain control over their financial footprint. Explore ecosystem guides on wallets, privacy coins, and routing strategies to refine your personal practices throughout 2026 and beyond.